Apache Syncope backend with Apache Karaf
Apache Syncope is an identity manager (IdM). It comes with a web console where you can manage users, attributes, roles, etc.
It also comes with a REST API allowing to integrate with other applications.
By default, Syncope has its own database, but it can also “façade” another backend (LDAP, ActiveDirectory, JDBC) by using ConnId.
In the next releases (4.0.0, 3.0.2, 2.4.0, and 2.3.7), Karaf provides (by default) a SyncopeLoginModule allowing you to use Syncope as backend for users and roles.
This blog introduces this new feature and explains how to configure and use it.
Installing Apache Syncope
The easiest way to start with Syncope is to use the Syncope standalone distribution. It comes with a Apache Tomcat instance already installed with the different Syncope modules.
You can download the Syncope standalone distribution archive from http://www.apache.org/dyn/closer.cgi/syncope/1.1.8/syncope-standalone-1.1.8-distribution.zip.
Uncompress the distribution in the directory of your choice:
$ unzip syncope-standalone-1.1.8-distribution.zip
You can find the ready to use Tomcat instance in directory. We can start the Tomcat:
$ cd syncope-standalone-1.1.8$ cd apache-tomcat-7.0.54$ bin/startup.sh
The Tomcat instance runs on the 9080 port.
You can access the Syncope console by pointing your browser on http://localhost:9080/syncope-console.
The default admin username is “admin”, and password is “password”.
The Syncope REST API is available on http://localhost:9080/syncope/cxf.
The purpose is to use Syncope as backend for Karaf users and roles (in the “karaf” default security realm).
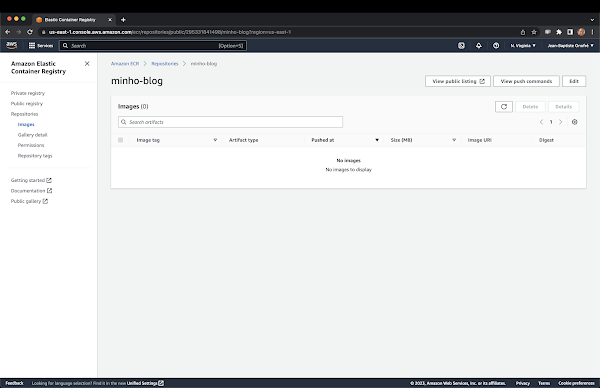
So, first, we create the “admin” role in Syncope:
Now, we can create an user of our choice, let say “myuser” with “myuser01” as password.
As we want “myuser” as Karaf administrator, we define the “admin” role for “myuser”.
“myuser” has been created.
Syncope is now ready to be used by Karaf (including users and roles).
Karaf SyncopeLoginModule
Karaf provides a complete security framework allowing to use JAAS in an OSGi compliant way.
Karaf itself uses a realm named “karaf”: it’s the one used by SSH, JMX, WebConsole by default.
By default, Karaf uses two login modules for the “karaf” realm:
- the
PropertiesLoginModuleuses theetc/users.propertiesas storage for users and roles (with user password) - the
PublickeyLoginModuleuses theetc/keys.propertiesas storage for users and roles (with user public key)
In the coming Karaf versions (3.0.2, 2.4.0, 2.3.7), a new login module is available: the SyncopeLoginModule.
To enable the SyncopeLoginModule, we just create a blueprint descriptor that we drop into the deploy folder. The configuration of the Syncope login module is pretty simple, it just requires the address of the Syncope REST API:
<?xml version="1.0" encoding="UTF-8"?><blueprint xmlns="http://www.osgi.org/xmlns/blueprint/v1.0.0" xmlns:jaas="http://karaf.apache.org/xmlns/jaas/v1.1.0" xmlns:ext="http://aries.apache.org/blueprint/xmlns/blueprint-ext/v1.0.0"> <jaas:config name="karaf" rank="1"> <jaas:module className="org.apache.karaf.jaas.modules.syncope.SyncopeLoginModule" flags="required"> address=http://localhost:9080/syncope/cxf </jaas:module> </jaas:config></blueprint>
You can see that the login module is enabled for the “karaf” realm using the jaas:realm-list command:
karaf@root()> jaas:realm-list Index | Realm Name | Login Module Class Name -----------------------------------------------------------------------------1 | karaf | org.apache.karaf.jaas.modules.syncope.SyncopeLoginModule
We can now login on SSH using “myuser” which is configured in Syncope:
~$ ssh -p 8101 myuser@localhostThe authenticity of host '[localhost]:8101 ([127.0.0.1]:8101)' can't be established.DSA key fingerprint is b3:4a:57:0e:b8:2c:7e:e6:1c:f1:e2:88:dc:bf:f9:8c.Are you sure you want to continue connecting (yes/no)? yesWarning: Permanently added '[localhost]:8101' (DSA) to the list of known hosts.Password authenticationPassword: __ __ ____ / //_/____ __________ _/ __/ / ,< / __ `/ ___/ __ `/ /_ / /| |/ /_/ / / / /_/ / __/ /_/ |_|\__,_/_/ \__,_/_/ Apache Karaf (4.0.0-SNAPSHOT)Hit '<tab>' for a list of available commandsand '[cmd] --help' for help on a specific command.Hit 'system:shutdown' to shutdown Karaf.Hit '<ctrl-d>' or type 'logout' to disconnect shell from current session.myuser@root()>
Our Karaf instance now uses Syncope for users and roles.
Karaf SyncopeBackendEngine
In addition of the login module, Karaf also ships a SyncopeBackendEngine. The purpose of the Syncope backend engine is to manipulate the users and roles back directly from Karaf. Thanks to the backend engine, you can list the users, add a new user, etc directly from Karaf.
However, for security reason and consistency, the SyncopeBackendEngine only supports the listing of users and roles defined in Syncope: the creation/deletion of an user or role directly from Karaf is disabled as those operations should be performed directly from the Syncope console.
To enable the Syncope backend engine, you have to register the backend engine as an OSGi service. Moreoever, the SyncopeBackendEngine requires two additional options on the login module: the admin.user and admin.password corresponding a Syncope admin user.
We have to update the blueprint descriptor like this:
<?xml version="1.0" encoding="UTF-8"?><blueprint xmlns="http://www.osgi.org/xmlns/blueprint/v1.0.0" xmlns:jaas="http://karaf.apache.org/xmlns/jaas/v1.1.0" xmlns:ext="http://aries.apache.org/blueprint/xmlns/blueprint-ext/v1.0.0"> <jaas:config name="karaf" rank="5"> <jaas:module className="org.apache.karaf.jaas.modules.syncope.SyncopeLoginModule" flags="required"> address=http://localhost:9080/syncope/cxf admin.user=admin admin.password=password </jaas:module> </jaas:config> <service interface="org.apache.karaf.jaas.modules.BackingEngineFactory"> <bean class="org.apache.karaf.jaas.modules.syncope.SyncopeBackingEngineFactory"/> </service></blueprint>
With the SyncopeBackendEngineFactory register as an OSGi service, for instance, we can list the users (and their roles) defined in Syncope.
To do it, we can use the jaas:user-list command:
myuser@root()> jaas:realm-listIndex | Realm Name | Login Module Class Name-----------------------------------------------------------------------------1 | karaf | org.apache.karaf.jaas.modules.syncope.SyncopeLoginModulemyuser@root()> jaas:realm-manage --index 1myuser@root()> jaas:user-listUser Name | Group | Role------------------------------------rossini | | rootrossini | | otherchildverdi | | rootverdi | | childverdi | | citizenvivaldi | |bellini | | managingDirectorpuccini | | artDirectormyuser | | admin
We can see all the users and roles defined in Syncope, including our “myuser” with our “admin” role.
Using Karaf JAAS realms
In Karaf, you can create any number of JAAS realms that you want.
It means that existing applications or your own applications can directly use a realm to delegate authentication and authorization.
For instance, Apache CXF provides a JAASLoginInterceptor allowing you to add authentication by configuration. The following Spring or Blueprint snippet shows how to use the “karaf” JAAS realm:
<jaxws:endpoint address="/service"> <jaxws:inInterceptors> <ref bean="authenticationInterceptor"/> </jaxws:inInterceptors></jaxws:endpoint> <bean id="authenticationInterceptor" class="org.apache.cxf.interceptor.security.JAASLoginInterceptor"> <property name="contextName" value="karaf"/></bean>
The same configuration can be applied for jaxrs endpoint instead of jaxws endpoint.
As Pax Web leverages and uses Jetty, you can also define your Jetty security configuration in your Web Application.
For instance, in the META-INF/spring/jetty-security.xml of your application, you can define the security contraints:
<?xml version="1.0" encoding="UTF-8"?><beans xmlns="http://www.springframework.org/schema/beans" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:schemaLocation="http://www.springframework.org/schema/beans http://www.springframework.org/schema/beans/spring-beans.xsd"> <bean id="loginService" class="org.eclipse.jetty.plus.jaas.JAASLoginService"> <property name="name" value="karaf" /> <property name="loginModuleName" value="karaf" /> </bean> <bean id="constraint" class="org.eclipse.jetty.util.security.Constraint"> <property name="name" value="BASIC"/> <property name="roles" value="user"/> <property name="authenticate" value="true"/> </bean> <bean id="constraintMapping" class="org.eclipse.jetty.security.ConstraintMapping"> <property name="constraint" ref="constraint"/> <property name="pathSpec" value="/*"/> </bean> <bean id="securityHandler" class="org.eclipse.jetty.security.ConstraintSecurityHandler"> <property name="authenticator"> <bean class="org.eclipse.jetty.security.authentication.BasicAuthenticator"/> </property> <property name="constraintMappings"> <list> <ref bean="constraintMapping"/> </list> </property> <property name="loginService" ref="loginService" /> <property name="strict" value="false" /> </bean></beans>
We can link the security constraint in the web.xml:
<?xml version="1.0" encoding="UTF-8"?><web-app version="2.5" xmlns="http://java.sun.com/xml/ns/javaee" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:schemaLocation="http://java.sun.com/xml/ns/javaee http://java.sun.com/xml/ns/javaee/web-app_2_5.xsd"> <display-name>example_application</display-name> <welcome-file-list> <welcome-file>index.jsp</welcome-file> </welcome-file-list> <security-constraint> <display-name>authenticated</display-name> <web-resource-collection> <web-resource-name>All files</web-resource-name> <description/> <url-pattern>/*</url-pattern> </web-resource-collection> <auth-constraint> <description/> <role-name>user</role-name> </auth-constraint> </security-constraint> <login-config> <auth-method>BASIC</auth-method> <realm-name>karaf</realm-name> </login-config> <security-role> <description/> <role-name>user</role-name> </security-role></web-app>
Thanks to that, your web application will use the “karaf” JAAS realm, which can delegates the storage of users and roles to Syncope.
Thanks to the Syncope Login Module, Karaf becomes even more flexible for the authentication and authorization of the users, as the users/roles backend doesn’t have to be embedded in Karaf itself (as for the PropertiesLoginModule): Karaf can delegates to Syncope which is able to façade a lot of different actual backends.







Comments
Post a Comment